Establishing a government-authorized computer center is a complex endeavor that necessitates meticulous planning and execution. This guide aims to provide a comprehensive overview of the essential steps involved in constructing such a facility, ensuring it adheres to all relevant regulations and requirements. From initial planning to deployment, this guide will illuminate the key considerations that govern the process.
- First it is crucial to define the scope and objectives of the computer center. This involves identifying the specific functions it will provide, as well as its target user group.
- , Subsequently, a thorough evaluation of existing infrastructure and resources must be conducted to determine any gaps or needs. This will help inform the design and arrangement of the computer center.
- , Moreover, it is essential to adhere to all applicable security measures to protect sensitive data and systems. This includes incorporating robust access controls, as well as regular security audits.
, Finally, ongoing support is crucial to ensure the smooth functioning of the computer center. This includes tracking system performance, resolving technical issues promptly, and introducing software updates regularly.
Conquering Regulatory Requirements for Government IT Infrastructure
Government departments are constantly adopting complex IT solutions to enhance governmental operations. However, this move often presents substantial challenges in meeting the stringent regulatory requirements that govern sensitive government data. A thorough understanding of these policies is essential for successfully navigating this complex landscape.
Failure to regulatory guidelines can result in serious consequences, like financial sanctions, termination of contracts, and loss of credibility.
Therefore, government IT professionals must prioritize regulatory compliance as a core priority in their plans. This requires a multi-faceted approach that includes implementing robust security controls, measures, safeguards, conducting regular audits and assessments, and educating staff on regulatory obligations.
Framework for Launching a Secure and Compliant Government Computer Center
Establishing a secure and compliant government computer center necessitates a meticulous blueprint that addresses every aspects of infrastructure, activities, and personnel training . This blueprint must outline clear protocols for data security , network surveillance , access restriction, and disaster restoration. Moreover, it should adhere with all relevant government mandates and industry best practices .
- Emphasizing a layered security strategy is crucial to reduce the risk of cyberattacks.
- Deployment of robust access systems is essential to avoid unauthorized access to sensitive data.
- Frequent vulnerability audits should be carried out to identify potential security gaps.
A comprehensive education program for staff is vital to enhance a culture of cybersecurity awareness. In conclusion, , the success of any government computer center depends on a well-defined blueprint that provides both security and adherence .
Best Practices Managing a Government-Authorized Computer Facility
Successfully managing a government-authorized computer facility requires strict adherence to best practices. A robust safety framework is paramount, encompassing physical entry, network isolation, and data encryption protocols. Frequent audits and vulnerability assessments are crucial for identifying gaps and implementing timely remedial actions. Comprehensive development programs for personnel ensure they understand their duties in upholding security standards. Furthermore, record-keeping of all system modifications and user behavior is essential for accountability and issue management.
- Enforce a strict change management process to minimize the risk of unauthorized modifications.
- Execute regular security assessments to identify potential threats and vulnerabilities.
- Preserve a secure physical environment with controlled access points and surveillance systems.
Securing Capital and Supplies for a Public Sector Computer Center
Acquiring the necessary resources to establish or maintain a public sector computer center is a crucial first step. These centers play an indispensable role in providing essential services to citizens, businesses, and government agencies alike.
A well-defined plan that clearly articulates the value of the computer center is paramount. This outline should detail the projected costs associated with hardware, software, staffing, and ongoing maintenance. To maximize the chances of success, it's essential to demonstrate a strong requirement for the center within the community and how it will contribute public service delivery.
Explore various funding sources, including:
* #Skill Local appropriations
* Private sector partnerships
* Crowdfunding campaigns
Remember to foster strong connections with key stakeholders, such as elected officials, community leaders, and business representatives. By effectively communicating the relevance of the computer center and its potential impact, you can increase your chances of securing the necessary funding and resources to make this vision a reality.
Enhancing Operations in a Government-Approved Computer Center
Within the rigorous framework of a government-approved computer center, refining operations is paramount. This complex environment necessitates a multifaceted approach that implements advanced technologies while adhering to robust security protocols. A key priority is to maximize resource allocation, affirming seamless operations and consistent service delivery. Additionally, continuous assessment of processes coupled with innovative initiatives are essential to maintain operational efficiency and compliance with evolving regulatory requirements.
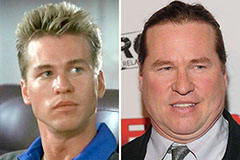 Val Kilmer Then & Now!
Val Kilmer Then & Now! Christina Ricci Then & Now!
Christina Ricci Then & Now!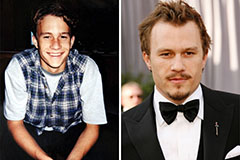 Heath Ledger Then & Now!
Heath Ledger Then & Now! Rachael Leigh Cook Then & Now!
Rachael Leigh Cook Then & Now!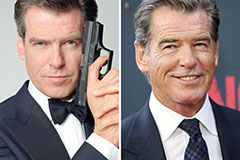 Pierce Brosnan Then & Now!
Pierce Brosnan Then & Now!